 |
BugnosisCopyright © 2000, 2001 Privacy Foundation. All rights reserved. |
Introduction
Web bugs are hidden surveillance devices in Web pages. Like cookies, they can be used to track your movements throughout the Web, but they are harder to spot. Bugnosis can help you find them.
Bugnosis operates by analyzing the Web pages that you visit while surfing. When it discovers a Web bug, it alerts you with a sound ("uh-oh!") and pops up a window containing details about the Web bug. It also makes visible the Web bugs hidden on the page, so you can see where they are placed. By revealing Web bugs, Bugnosis makes it possible for ordinary Web users to "watch the watchers."
Bugnosis is an educational tool, not a Web bug blocker. For more information, visit the Bugnosis FAQ site.
Bugnosis has been designed to work on PCs running Microsoft Windows and Internet Explorer. You'll need Windows 98 or newer, along with Internet Explorer version 5.5 or newer.
 The Bugnosis Toolbar
The Bugnosis Toolbar
Bugnosis is controlled through its toolbar, pictured here. The drop-down
menu on the left edge gives access to various settings.
![]() The bug image is a toggle
switch that controls whether the details/analysis window pane is visible or not.
That window might pop up by itself sometimes too, according to your settings.
The bug image is a toggle
switch that controls whether the details/analysis window pane is visible or not.
That window might pop up by itself sometimes too, according to your settings.
The four boxes to the right of the bug are a meter that show how suspicious the Web bugs on the page seem to be. The current view shows 3 boxes of severity for the current page. It's a very simple graphic that is either hollow gray (nothing unusual), partly yellow (somewhat suspicious) or yellow and red (Web bugs found). Summary information is given in the text on the right. The details about the elements on the page are reserved for the analysis window, which will be explained below. But first a word about how Bugnosis works.
Identifying Web Bugs
Bugnosis tags each element it encounters with a list of properties, described below. Then Bugnosis decides whether the properties, taken together, suggest that the element is a Web bug. The procedure it uses is controlled in part by settings in the Bugnosis options menu.
Tiny means that the image takes up a very small amount of visual space on the screen, suggesting that the Web designer who placed it intended to hide it from view. Generally speaking, an image will have to be tiny for Bugnosis to designate it a Web bug. But tiny images are also used by Web developers to control the visual layout of a Web page, so an image can be tiny without being a Web bug.
Once means that the image is only used once within the document. This property helps to distinguish tiny images that are used for tracking of users and those that are used to control the visual layout of the Web page (see Tiny).
Domain means that the image comes from a different domain than the original Web document. This suggests that a third-party computer may be tracking the users that visit a particular Web site. An image usually has to come from a different domain to be identified as a Web bug.
Cookie means that the URL for the image overlaps significantly with information stored in a cookie. This may suggest that a Web site is "synchronizing cookies," i.e., sharing data about you with another Web server.
Lengthy means that the URL for the image is unusually long and may contain more information than is usually necessary for simply retrieving the image from the Web server.
Protocols means that the URL for the image contains more than one protocol field
(i.e.,
TPCookie means that the image comes from a different domain than the document and manipulates a cookie (Third Party Cookie). Third party cookies can be used to track users across multiple Web sites.
Recognized means that the URL for the image is in Bugnosis' list of "well known" Web sites, some of which are known to be Web bug users, and some of which are known not to be Web bug users.
Sample Output
Here's what Bugnosis showed us one day when we visited www.wired.com.
Highlighted images may be Web bugs. Highlighted images are suspicious.
The first line describes a very suspicious image from DoubleClick.net embedded within the www.wired.com page. The image has the "Tiny", "Once", "Domain", and "TPCookie" properties. Based on this evidence, Bugnosis concludes that this is probably a Web bug, colors the entry red, and says "uh-oh!" Note that the value of the third party cookie (id=80000021cc37be5) is displayed here too. This number is DoubleClick's identifier for the user who visited CBS.com. This single line of Bugnosis output shows that when the user went to the Wired News home page, his own computer was secretly enlisted to tell DoubleClick.net that he went there.
The first line also includes the
![]() icon. By clicking on it,
the user can navigate to DoubleClick's privacy policy. Bugnosis doesn't have this
information for every site -- if you look at the third line, you will see that it doesn't
even know how to find the privacy Web page for lycos.com. Still, finding those pages is usually
pretty straightforward -- just go to the site's main page and look for a privacy link. They
are often at the bottom of the page.
icon. By clicking on it,
the user can navigate to DoubleClick's privacy policy. Bugnosis doesn't have this
information for every site -- if you look at the third line, you will see that it doesn't
even know how to find the privacy Web page for lycos.com. Still, finding those pages is usually
pretty straightforward -- just go to the site's main page and look for a privacy link. They
are often at the bottom of the page.
The second line colored in yellow is a reference to a JavaScript program, not an image: that's what the "Script" prefix means in the "Embedded URL" column. These types of elements can also be used to transmit tracking information (most Web elements can), but Bugnosis isn't able to even guess whether that's part of their purpose or not. So, Bugnosis never colors these elements red -- it considers them merely "suspicious".
The third line, with a white background, shows an ordinary image on the page. Note that you see a squashed version of the image as painted on the display: in this case, you can barely make out the text "LOG IN". You don't see any such images on the other lines, either because their images are not actually visible (that's one of the distinguishing features of a Web bug) or because they're not images at all.
The final image is also invisible, but it's a large image, with no associated cookie, that appears multiple times on the page. Bugnosis concludes that's a completely innocuous "spacing" image used for alignment purposes. In fact, Bugnosis will normally not even show you these images, since they're so routine. Unless you change its options, Bugnosis will only show the Web bugs in red and the suspicious images in yellow, and it will omit all of the others. (The original page had many more such innocent entries, but we manually removed them from this example for brevity.)
When Bugnosis is running, you can click on the [Details] links for more technical information about the element in question, but they don't do anything in the example above.
Options
Click the Bugnosis drop down menu in the Internet Explorer tool bar. Most of the choices (Save, Send to, Print, About) are pretty straightforward. You can also select Options to configure Bugnosis.
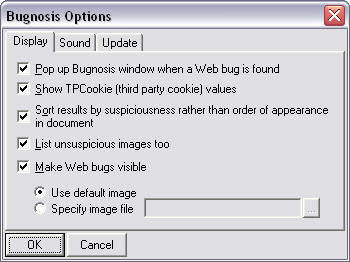
- Pop up Bugnosis window when a Web bug is found. If this option is selected, then Bugnosis will make itself visible whenever it detects a Web bug. Otherwise, Bugnosis will never automatically make itself visible, and you will have to click the icon on the Internet Explorer toolbar if you want to see the Bugnosis analysis of a Web page. Changes to this option become effective when you load a new Web page.
- Show TPCookie (third party cookie) values. Sometimes the TPCookie values can be very long, making the results table hard to read. This option lets you turn off the TPCookie display if you want.
- Sort results by suspiciousness rather than order of appearance in document. When selected, this option puts the images most likely to be Web bugs at the top of the list. Otherwise, the images are displayed in the order they appeared in the document.
- List unsuspicious images too. Normally Bugnosis only displays details about the images that it has labeled Web bugs or suspicious.
- Make Web bugs visible. When Bugnosis detects a Web bug, this option will make it
turn the image that is trying to hide into a clearly visible one (
 by default)
so you can see where the bug was
planted on the page. Sometimes you will find that Web bugs are planted next to other information
that suggests what the bug may be used for.
by default)
so you can see where the bug was
planted on the page. Sometimes you will find that Web bugs are planted next to other information
that suggests what the bug may be used for.
The two other tabs on the options dialog ("Sound" and "Update") lead to these choices:
- Play sound when a Web bug is found. When selected, this option makes Bugnosis play a sound when it discovers a Web bug. Otherwise, it will remain silent.
- Update DB. Click to immediately download the latest database from the Bugnosis Web site. This mostly helps keep the list of Web site contacts up to date. It also gives us a mechanism to send you a message (e.g., announcing a new version) when you click update. But note that this doesn't update the Bugnosis software.
- Remind me to download new rulesets after... Disable this option if you are not interested in being reminded to fetch ruleset updates from our Web site.
Getting and Installing Bugnosis
Visit the Bugnosis Web site for installation instructions.Uninstalling Bugnosis
First, note that you can disable the Bugnosis sound, and you can make it stop popping up, just by changing the Bugnosis options. If you still want to uninstall, just choose the "Uninstall" context menu entry that you'll see when you right-click in the Bugnosis window.
Feedback
Please use the e-mail address privacy-tools@cs.du.edu for questions, comments, suggestions, and bug reports related to Bugnosis. We can't guarantee a personal response, but we read all of the e-mail that gets sent our way.
Credits
This software was written by Adil Alsaid at the University of Denver Department of Mathematics and Computer Science under the direction of Prof. David Martin.
Bugnosis uses the "uh-oh" sound kindly provided by Ipswitch, Inc.
Bugnosis contains the Regex++ library:
Regex++ version 3.02, 18 April 2000 Copyright (c) 1998-2000 Dr John Maddock
Copyright © 2000, 2001 Privacy Foundation. All rights reserved. "Bugnosis" and the "cute bug" icons are registered trademarks of the Privacy Foundation. The Bugnosis software carries no representation or warranty with respect to functionality, merchantability, or suitability for a particular purpose, nor any other representation or warranty whatsoever. Bugnosis users assume all risk associated with the application.